Prevent Double Human
World ID Lift Off | San Francisco | April 17, 2026
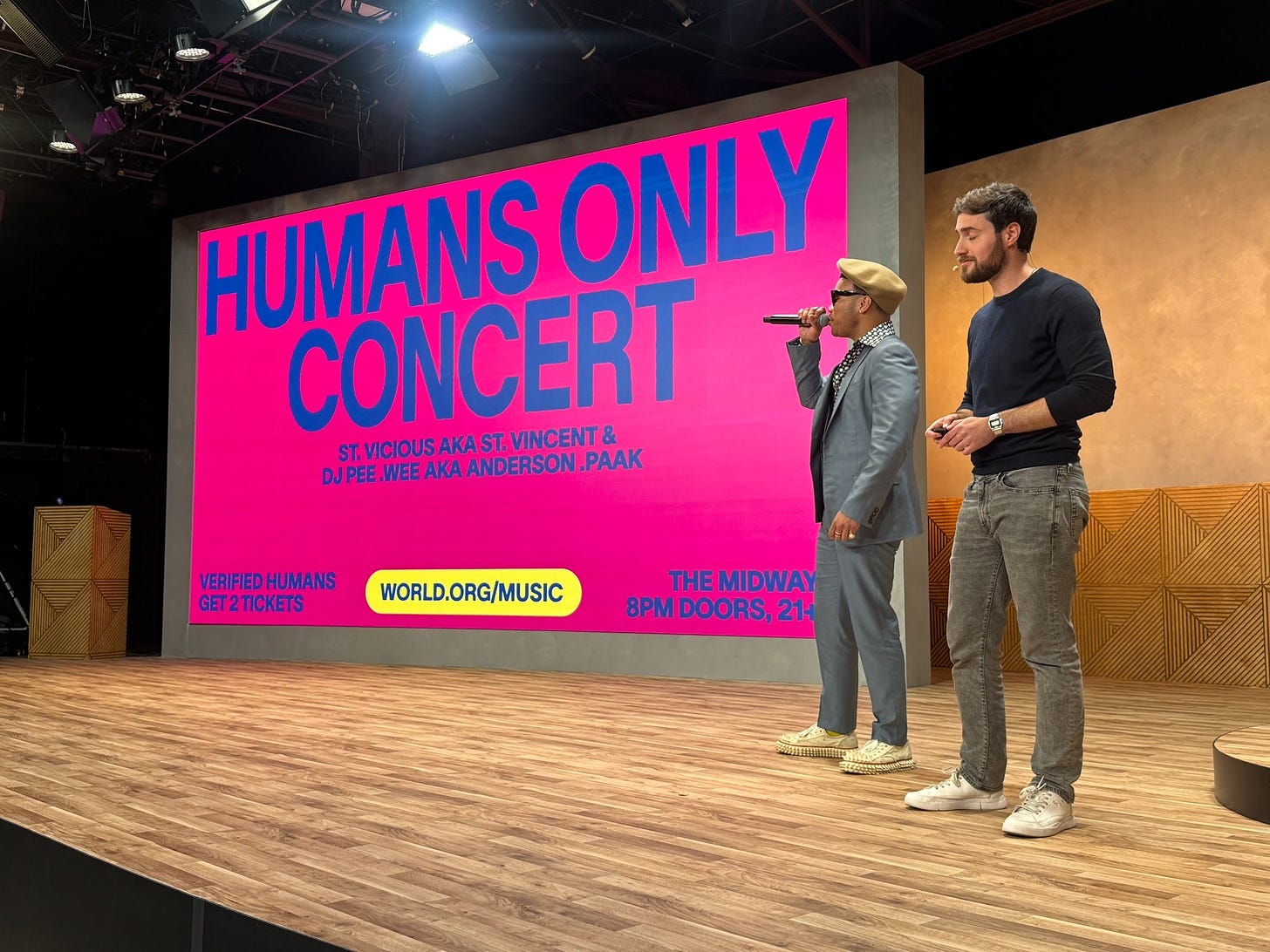
Participating in World Day on Friday, April 17, 2026, in San Francisco, was a watershed moment for us as students at the intersection of emerging technologies, gaming, and entertainment. In contrast to the general fear that AI often incites in Hollywood, gaming, and artist circles, we felt a new sense of hope that humans matter in the age of AI. When music artist Anderson .Paak stepped on stage to support the World technology because he wants to support a future that prioritizes humans, one can feel that something different is happening here. We believe in this hope and the idea that we are on the precipice of leapfrogging the current internet in terms of transparency and authenticity, all driven by a new layer of the internet, a real human layer. We always say that AI pours gasoline on the fire of inauthenticity, and that Cambridge Analytica will look small in terms of impact compared to the nefarious impact of deepfakes in our new AI world. In short, World’s new World ID 4.0 and the many enterprise announcements and key learnings of the day warranted a special sidebar from our three-part series on age-verification in gaming. Below is what transpired at the World gathering, along with the process of completing the WorldID Verification.
Beyond Data Collection: A Real Human Network and Zero-Knowledge Proofs
As gaming and media companies face mounting regulatory pressure to age-gate their services, we believe platforms should be able to answer an even simpler question - is this user human? Our initial report, titled “Age Rage Beyond Roblox | Online Age Verification Becomes the Norm,” concludes that age verification is inevitable, but the current attempts to regulate internet access may ignore the importance of a privacy-first approach. Since then, we have continued the discussion in our weekly live stream, across investor and studio meetings, and on a GamesBeat Panel at GDC 2026. We continue to revert to the same question - before verifying a user’s age, how will we first resolve the “proof of human” question? In an AI world, this is of tantamount importance given the prevalence of bots, replicas, and AI agents acting on others’ behalf. This was addressed in our second report titled “Beyond Age Verification: Proof of Humans (and their AI Agent Circles of Trust).”
Walking into World Day, San Francisco
Stacks of newspapers titled, “A Real Human Network: The Case for a Human First World in a Post-Human Internet” explain the key message of the day. There is no author. On the back, at the bottom, there is a single line - “Circulated in San Francisco, California. 2026.” It starts,
“Soon, the internet will no longer assume you are human. This will deeply affect how we trust one another, how we interact, and even whether we are recognized as human at all. Humans have always needed ways to recognize one another. Throughout history, as technology advanced we invented ways to prove individual presence: a carving on a cave wall, a stamp pressed into wax, a signature on paper. Each expressed the same simple idea: I am here. I am real. And this assumption followed us into the digital age. In the world of the early internet we carried that trust with us, believing that behind every interaction was a person, a digital reflection anchored to a living, breathing human being. That era has ended. For the first time in human history it is becoming clear that intelligence will soon be abundant. And with it, the ability to generate convincing human presence online. Already, a large share of internet activity is automated, and very soon the majority of online interactions will not involve humans at all. How do we remain visible to each other in a world where human presence is no longer the default or even reliable assumptions? To answer this question the internet may need a new layer: a real human network.”
The gathering was open to the public and packed with curious technologists, investors, enterprises, and even cypherpunk tinkerers. Entering the building, Orb devices lined the walls.
Step 1. Scan your iris using an Orb device. Hold your phone next to the device to watch the device transfer the data to your phone, followed by a deletion from the Orb device.
Step 2. The Orb creates a unique biometric identifier that will be recognized as human when it transacts online. No ID or even name was given in the process. What about AI agents, deployed by humans? AgentKit, first announced on March 17th, allows verified humans to delegate their World ID to AI agents, making them human-backed agents. A world in which we designate agents to transact online on our behalf is no longer a sci-fi idea for the future. As these online transactions accelerate, surely we will demand certainty on these agents’ actions and the human that directed them. McKinsey projects it could reach $3 to $5 trillion globally by 2030. Bain estimates AI agents could account for up to 25% of all U.S. e-commerce by 2030.
Major Enterprise Announcements
After Co-Founder Sam Altman kicked off the day with an inspirational overview of the strategy, a drumbeat of new enterprise announcements followed. First, Tinder described the urgency in identifying humans-only for the relationship app, and offered World ID-verified Tinder users five free “boosts” to increase profile visibility. One can imagine this verification becoming table stakes, for Tinder and for its users, along with its competitors. Next, DocuSign announced that the company will adopt World ID, explaining the practical reality and high risk of a growing set of fake signatories. Finally, Zoom gave the most compelling showcase with its CEO, who was marked with the equivalent of a “blue check mark,” alongside a couple of “fake” Alex Bhanias, the CEO of Tools for Humanity.
Finally, Concert Kit wowed the crowd, as Anderson .Paak came out onstage to say that he wants humans at his concerts. From now on, there will be a carve out of tickets only for verified humans, not bots.
Monetization Announced
The company published a blog post describing the future revenue model for World ID 4.0. In short, enterprises that find it in their interest to know whether their customers are human will pay for each of their users. While it has not yet been activated, we believe this lays the groundwork for a portion of this fee to be paid in the future to the World Network. What we like about this is that the revenue model fits with our #1 mantra - merge onto the highway of behavior that is already happening. In other words, the revenue flow to World does not require any change in user behavior. This should, if executed well, be a win-win-win for World, enterprises, and their customers.
Zero-Knowledge Proofs
We have long believed that the optimal privacy-first solution for age verification is a cryptographic technique known as zero-knowledge proofs (ZK proofs), which is now widely used on blockchain networks. Zero-knowledge proofs were first introduced in a 1985 MIT paper by Shafi Goldwasser and Silvio Micali, titled “The Knowledge Complexity of Interactive Proof-Systems.” The paper defines zero-knowledge proofs as “proofs that convey no additional knowledge other than the correctness of the proposition in question.” The core principle of a ZK proof is that most information requests can be satisfied with a simple Yes or No answer: Is this true or not? Typically, one discloses more information than is needed.
In the 1990 paper, “How to Explain Zero-Knowledge Protocols to Your Children,” Quisquater et al. illustrate how ZK proofs work through the “Cave of Ali Baba.” Imagine a circular cave (see Figure 1) with a single entrance and two paths that meet but are blocked by a magic door. Person A, the prover, tells Person B, the verifier, “I know the secret code to open the door, and I am willing to sell it to you,” but Person B asks, “Well, how do I know it’s real?” Now they are stuck because Person A won’t give Person B the code without payment, and Person B won’t pay until they are sure the code is correct. So they create a test: Person A will go into the cave alone and choose to go down either the right or left path. Then Person B enters the cave and randomly asks Person A which path to exit from. If Person A truly knows the secret code, it doesn’t matter which path Person B chooses because they can pass through the magic door. Repeat this test enough times, and statistically, the verifier becomes certain that the prover knows the secret code, while learning nothing about what the code actually is. In other words, the core idea of zero-knowledge proofs is certainty without disclosure.
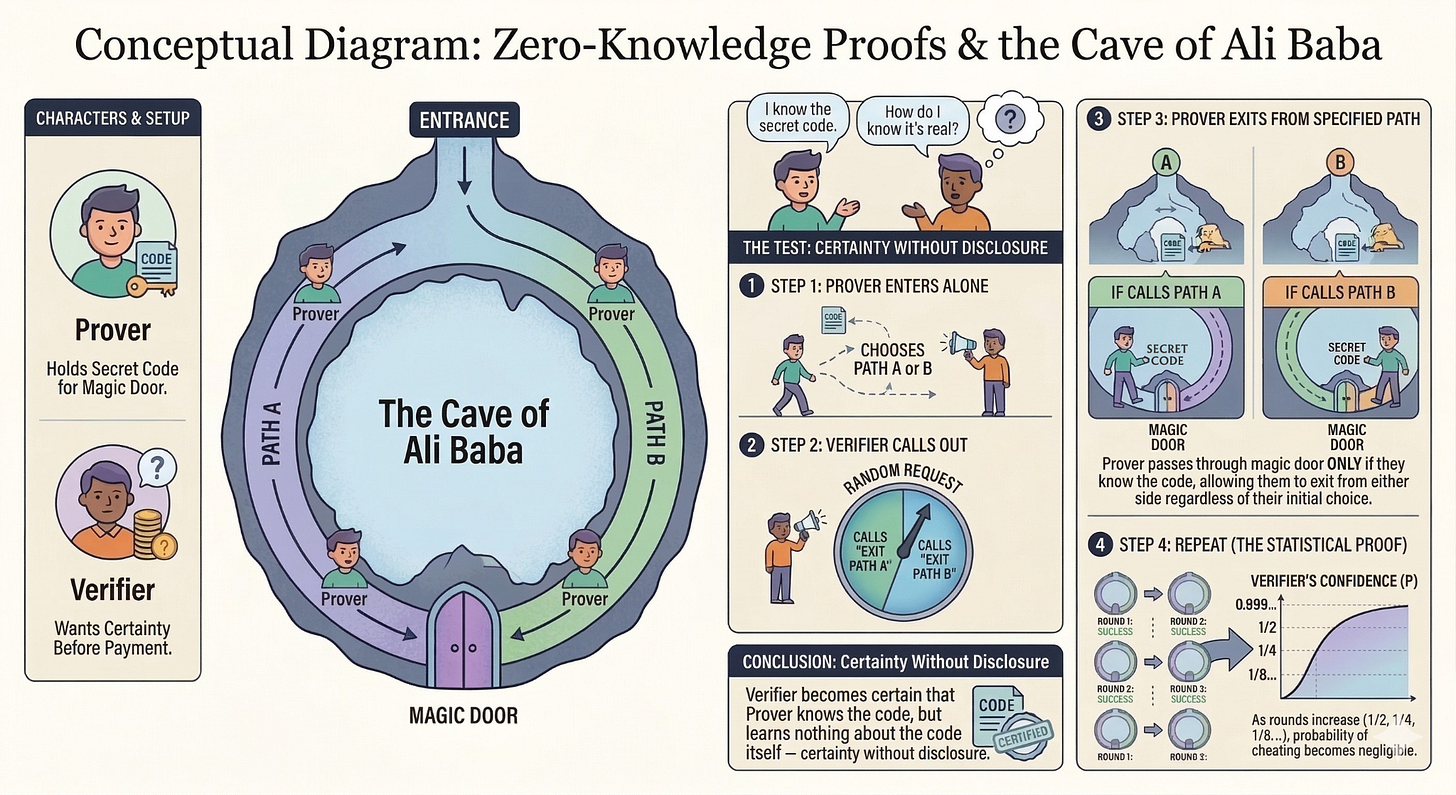
How does it work in the digital world? The cave becomes a mathematical challenge that is easy to verify but nearly impossible without “the secret code” or a piece of data. Instead of physically walking around a cave, the prover’s own device is running thousands of checks to confirm the data without ever revealing it; meanwhile, the verifier’s computer checks the answers instantly, achieving the same statistical certainty described by the cave example. The mathematical problem is solved without ever needing to provide the actual data. This statistical certainty is all that is needed to answer whether you are human and if you are age-appropriate.
Key Risk - The Flipside of Using a Strong Biometric
World uses the iris for proof of human because “the iris code generated from a scan of a human eye can have over 200 bits of entropy, significantly more than the entropy contained in a fingerprint scan [and] around four orders of magnitude (10,000x) more accurate than facial recognition due to a higher entropy in the iris structure compared to the face.” Even identical twins can be easily distinguished. The main risk is that biometric data is not replaceable. A password can be changed, but a biometric marker cannot. For this reason, there are many regulations around the process. For example, the Orb device is only allowed to be used if one is at least 18 years old. The scanner accurately determines the age of one’s iris. According to our Orb trainer, the only challenging age is 18, plus or minus a couple of years. There are ways to prove that one is over 18, but the company discourages this due to its preference not to collect PII.
Alternatives to Proof of Human
World’s adoption of ZK-Proofs is what makes this technology particularly compelling for privacy protection, but there are alternative approaches to online identity verification. Each alternative below tackles different aspects of the problem, such as security, privacy, or accessibility. However, the key question remains whether any of these solutions can address the fundamental issue in a post-human internet: demonstrating proof that a unique human is behind an interaction.
Passkeys
Passkeys offer users a way to replace passwords by storing a cryptographic key directly on their device. The key is unlocked by a fingerprint or face, sending a mathematical proof to the website instead of your password. Apple and Google have already deployed passkeys at scale and represent a meaningful improvement over password-based logins. No passwords are stored on a server, largely eliminating phishing attacks.
While passkeys allow for a more secure login, their fundamental design limits their use as proof of personhood, since they demonstrate that a user controls a specific device, not that the user is uniquely human. A single person could register passkeys across a hundred devices, which could appear as a hundred distinct users. For everyday logins, the ability to distinguish between users is irrelevant; however, for anti-bot systems, age verification, and proof of personhood, it is the central problem they were not designed to solve.
Government Digital IDs
Government Digital IDs are an interesting solution because, in theory, they would enable standardized online verification. If executed correctly, it would enable uniform rules for data collection, plug-in systems for developers and platforms, and legal accountability. However, as seen over the last few months with most age-verification laws, governments tend to prioritize quick legislation over comprehensive policy.
This past week, the EU announced a breakthrough step toward a centralized age verification system controlled by a government body and described the app as “ready for deployment.” stating, “the new age verification app is user-friendly and can be set up using a passport or ID card, enabling users to prove their age when accessing online services. The app is completely anonymous, works on any device, and is fully open source, meaning partner countries around the world can also adopt it.” We believe a privacy-first approach will ultimately win, so the EU’s promise of anonymous verification was intriguing. However, within hours of encouraging people to explore the open-source code, security experts raised concerns.
Security consultant Paul Moore demonstrated a full bypass of the app’s security in under two minutes. In his posts on X, he highlighted two flaws. The app stores the user’s PIN in a plain, editable file on the device rather than in the hardware-level Secure Enclave found on every modern smartphone. Moore was able to reset the PIN by simply deleting two values from that file and gained full access to the original identity credentials. The second flaw - the entire biometric verification system was controlled by a single true/false switch in the same editable file. This meant Moore could change a single value, and the app would skip biometric checks entirely. According to these reports, the root issue with the EU’s app is an antiquated software-level solution rather than a more advanced hardware/smartphone integration.
Beyond technical issues, there is a fundamental concern about governments serving as the trusted issuer, which extends beyond whether it is trustworthy today. A system designed by a privacy-conscious government today can be inherited by a different administration tomorrow, which can expand the scope over time in ways its architects never intended. The infrastructure persists even when intentions change.
Decentralized Wallets
Decentralized wallets allow users to securely store verified credentials on their devices and present only what is needed for a specific interaction. Spruce ID and Polygon ID are two examples of solutions that incorporate ZK proofs to enable selective disclosure. The wallet itself is not the verification; it is the delivery mechanism. Meaning the wallet is only as good as the credentials stored within it. Our physical wallets do not actually allow us to purchase anything or prove that we can drive a car; the credit cards and driver’s licenses provide these verifications. The decentralized wallet provides the necessary data security once verification is complete, but it is not involved in the initial verification.
Each of these alternatives was designed to address part of the problem. Passkeys eliminate passwords for proving device control but not for proving human uniqueness. Government digital IDs offer much-needed standardization but also introduce surveillance risks. Decentralized wallets enable selective disclosure but leave open the question of a trusted issuer and multiple identities, challenging in an AI-agent world. Hardware identity devices, like YubiKey, provide strong physical security but face challenges of dedicated hardware, inaccessibility at scale, and loss or theft. Each alternative touches a part of the problem but none were built to ascertain personhood.
A Note from Angela Dalton, Signum Growth | AD8 Pop - Being at the World Lift Off gathering as a human was truly awesome. The vibe was in stark contrast to the typical gaming or media gathering in which artists and developers speculate, in fear, about the impact of AI on their lives. Anderson .Paak’s comments resonated - World ID’s AI-related technology inspired a creator to ‘get involved’ and share a message of hope that it is not too late, even in an AGI world, for humans (and our agents) to act as the orchestrators of our future. We started this exploration in response to Roblox’s child safety headlines and the overall challenge that faces the gaming and social media platforms. It is abundantly clear to us that before solving age verification, we must first build a new foundational layer into the internet that ranks humans above all transactional actors on the internet. This will come from our ability or inability to answer one simple question - are you human?