Bits of Gaming Chapter 2 | The Axie Infinity Hack
The Importance of Weakest Links, Decentralization & the Promise of Polkadot (Security and Interoperability)
In this $625 million attack, one of the largest in history, the important numbers are 5 out of 9. Regardless of how many impressive quantitative metrics and complicated technical reports that one may come across in trying to understand blockchain protocols, this hack comes down to the fact that its attackers successfully compromised only 5 out of 9 validators in Axie’s Ronin network, a sidechain of Ethereum. Only a year ago, Axie Infinity grabbed headlines when it was seeing more revenues than Ethereum itself. So what happened and from a blockchain gaming perspective, what can we learn from this?
Going back to 2017/2018
We left the traditional world to focus on gaming meets NFTs, inspired by the elegance of Bitcoin and the idea that gamers have been buying, selling and trading digital assets for decades. However, it was frustrating to try to figure out how Ethereum would actually work in the traditional gaming world, made up of 2.5 billion gamers. The three major hurdles in my assessment were 1) the nuisance of buying a token to do every transaction; 2) the idea that more people joining the game (= good), means that transactions get more, not less, expensive as more players join; 3) slow speeds of 15 transactions per second for Ethereum didn't seem to fit with the current expectations set by AAA stalwarts like Call of Duty or Fortnite (I didn’t even have rug pulls in my top three concerns). So it was a major breakthrough when sidechains, bridge networks, rollups, ZK Snark rollups and the like came along. The promise was open, almost-toll-booth-free frontage roads running alongside a crowded highway, giving the ability to cruise at high speed, and then merge back onto the highway at the destination.
Sidechain definition: According to Ethereum.org, a sidechain is a separate blockchain which runs in parallel to the Ethereum Mainnet and operates independently. It has its own consensus algorithm, which is the way that blockchain networks come to a general agreement on transactions—at least 51% of the nodes on the network must agree on the next global state of the network. A sidechain is connected to the Mainnet (in this case Ethereum) by a two-way bridge, but the main network does not verify the integrity of the sidechain; it relies on the sidechain’s set of validators to attest validity.
Ethereum is currently going through a migration from Ethereum 1.0 to Ethereum 2.0. ETH 1.0 is the current mainnet chain, which, similar to Bitcoin, uses Proof of Work (PoW) to validate transactions. Ethereum’s current “hash rate”, a measure of the compute power which is dedicated to verifying transactions and adding new blocks to the network, is 1.07 PH/s. In an effort to avoid a technical discussion, we will just point out that it is close to an all time high and second only to Bitcoin in energy consumption.
Ethereum validation will migrate to use Proof of Stake (PoS), requiring much less energy, similar to Polkadot, Tezos and others. (Side note: Energy usage is not the topic of this report but just a comment on Bitcoin since it is a hot topic - we hear the energy usage criticisms but this is what makes Bitcoin so secure. Also, on the margin many factors are improving.) Back to Ethereum’s transition to 2.0, there are 329,586 validators on ETH 2.0 as of April 2. Importantly, even though the Axie Infinity game runs on an Ethereum sidechain, none of the Ethereum Mainnet’s security mechanisms protect against an Axie Infinity hack because Axie depends on the security of the sidechain, Ronin, not on Ethereum itself. Ronin, relying on only 9 validators, most of whom worked for the company, provided security for more than a billion dollars, which made the chain a target for these malicious actors.
The funds from the Ronin attack were specifically drained from the Ronin Bridge; bridges interact with validators from two different networks and have proven especially vulnerable to large scale attacks. The chart below depicts several of the larger attacks on blockchain bridges, in which hackers have successfully siphoned more than 1 billion dollars of funds from unassuming networks.
Vitalik Buterin, Founder of Ethereum, gave the world a prescient warning two months ago that these applications are unsafe. He started the post point blank,
“..while I am optimistic about a multi-chain blockchain ecosystem, I am pessimistic about cross-chain applications”
And then he further explained that it is better to keep Ethereum apps on Ethereum and Solana and other protocols’ apps on their own native protocols. He gave an example of moving 100 ETH onto a bridge on Solana -
“Even if there's a perfect ZK-SNARK-based bridge that fully validates consensus, it's still vulnerable to theft through 51% attacks.”
We have touched on sidechains and bridges. What about rollups? Vitalik Buterin succinctly continues -
“This incidentally is also why a rollup can't just "go use another data layer". If a rollup stores its data on Celestia or BCH or whatever else but deals with assets on Ethereum, if that layer gets 51% attacked you're screwed. The DAS on Celestia providing 51% attack resistance doesn't actually help you because the Ethereum network isn't reading that DAS; it would be reading a bridge, which would be vulnerable to 51% attacks. To be a rollup that provides security to applications using Ethereum-native assets, you have to use the Ethereum data layer (and likewise for any other ecosystem).”
Going back to Bits of Gaming: Chapter 1 on February 7th, despite our original excitement for all things gaming meets NFTs, we believe there is a lot to fix before crypto is ready for AAA gaming. The skeptical tone among gamers is reminiscent of their “no thanks” attitude to other money-extracting attempts in past gaming cycles, e.g. in-game advertising and pay-to-win. As Discord CEO Jason Citron commented when asked if the company would be entering crypto -
We’re excited about the potential for web3 technology and the positive ways these communities are coming together on Discord, especially those organized around environmentally friendly, creator-focused projects. However, we also recognize there are some problems we need to work through. For now we’re focused on protecting users from spams, scams and fraud.
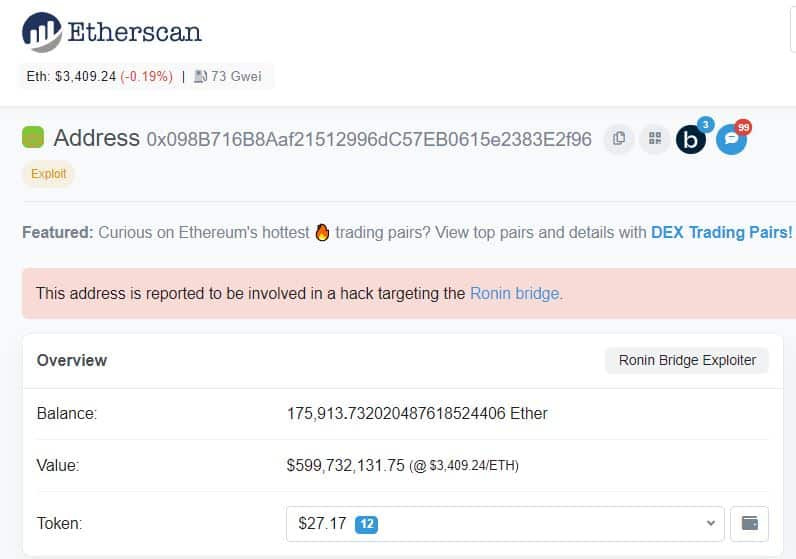
The good news about the Axie Infinity hack is that thanks to the inherent transparency of blockchain technology, the location of the stolen funds is fully traceable. In fact, here is the wallet open for the public to see! I would imagine that the company, its investors, Chainalysis, the FBI and many others in the crypto community will be watching for any movement, which could ensnare the players in their heist. This fact, in and of itself, should help deter future hackers.
The Promise of Polkadot
Going back to our initial research into blockchain gaming technology in 2017/2018, we stumbled upon Polkadot, which seemed to address all of the AAA gaming (and other mass market application) hurdles mentioned above: 1) requiring a token for all transactions; 2) the idea that if hundreds of millions of people want to play a game, the network will get really clogged and transactions will become prohibitively expensive; 3) slow speeds. The Axie Infinity hack gives us a reason to revisit a few aspects of Polkadot.
As background, Gavin Wood, Co-Founder and CTO (lead coder) of Ethereum and inventor of Solidity coding language and the EVM (Ethereum Virtual Machine), set out in 2016 to create a generalized, vertical agnostic, fully decentralized network that would be future-proofed. It would not compete with other blockchains but would provide a new Layer 0, operating one layer below Layer 1 blockchains like Ethereum and Bitcoin. It would have high speed (transaction throughput) also it would not require tokens as networks could inherit the security of the wider Polkadot umbrella.Just as many of our Web2 actions do not require payment (e.g., Google searches), the future version of the internet, Web3, will prompt many actions that will seem strange to pay for. Smart contract protocols would be possible in the Polkadot ecosystem, but Polkadot itself is not a smart contract protocol because, again, not everything we will be doing online in the future will require a smart contract. Polkadot’s purpose - to provide an air-tight, fully decentralized security mechanism (Polkadot’s Relay Chain) for all to access. Note: The final phase of the Polkadot roll out finally occurred on December 21, 2021, five years after inception.
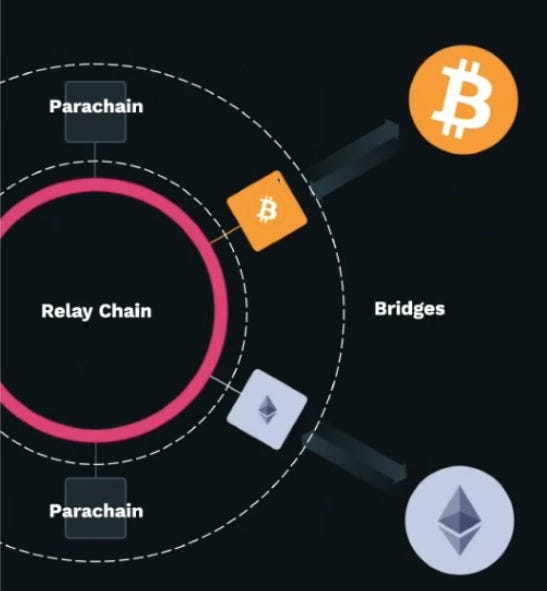
Visualizing Polkadot
For a deeper dive into the Polkadot tech, Polkadot Founder Rob Habermeier wrote a detailed overview in January of this year. He explains that Polkadot is a sharded blockchain with heterogeneous shards. Put another way, this means that the Polkadot validator set can understand transactions and network states from connected blockchains, even if they vary in design. If they are Polkadot chains, they are known as parachains. Some parachains will provide functionality that will be used by all other chains, and these will be referred to as “common good” chains. Once these very different (heterogeneous) blockchains attach to Polkadot, they will receive security and messaging functionality, or the ability to communicate, or interoperate, between each other. The most helpful visual of the architecture that we have seen is below.
The Polkadot Network hosts and secures other protocols; it does not to replace incumbents like Ethereum
The Polkadot Network facilitates cross-chain transfers of assets and application logic
The Polkadot Network and its native DOT token allow third parties to interact with all parachains and other blockchains
Polkadot Validators
In the context of Ethereum 2.0’s 300k+ validators and Ronin’s 9 validators, Polkadot will start its network with 1000 validators, and scale to greater numbers as the Polkadot ecosystem grows. One might ask why Polkadot is only starting with 1000 versus hundreds of thousands.
First, the validator selection mechanisms are different between Polkadot and the future Ethereum 2.0 because Polkadot can provide strong availability and validity guarantees with a smaller number of validators per shard. First, randomness determines which parachains validators are verifying, reducing the risk of collusion. Also, as explained on polkadot.js, validators in Polkadot are not the only stakers; including these, the number can scale up to hundreds of thousands. Since validators are performing critical consensus work to maintain the security of all of the blockchains running in its ecosystem, a more modest number of validators is needed to start as parachains only just started rolling out a few months ago. Kusama, Polkadot's canary network (Kusama is not simply a test net since real value is at stake) currently has 900 validator slots in the active set.
Finally, it is worth noting that there are different definitions of validators between protocols. Some networks count validators as remote signing keys that don't have the full operation of a validating node. On Polkadot, each validator is running its own validating node and performing full verification of the Relay Chain, voting on finality, producing blocks in their decided slots, and verifying parachain state transitions. Also, other protocols may consider validators and "validating nodes" as separate entities, while Polkadot considers this one.
What about 51% attacks on Polkadot?
The Axie Infinity hack certainly raises the question. As the Polkadot Wiki explains, 51% attacks will not be possible, because the disparity between chain security will not be present. When a parachain connects to Polkadot, the Relay Chain validator set becomes the securer of that parachain's state transitions. The parachain will only have the overhead of needing to run a few collator nodes to keep the validators informed with the latest state transitions and proofs/witness. Validators will then check these for the parachains to which they are assigned. In this way, new parachains instantly benefit from the overall security of Polkadot even if they have just been launched.
How Big is the Polkadot Developer Community?
In 2021, Polkadot was the second largest developer community, behind Ethereum; developer growth was up ~60% YoY.
Source: Electric Capital Jan 2022
And Polkadot reached more monthly active developers faster than other networks.
Source: Electric Capital Jan 2022
So why haven't I heard of it? The biggest criticism of Polkadot is its lack of marketing.
Founder Rob Habermeier’s Final Words Embody the Ethos of Polkadot
The mass media of the internet encourage messages of building, primarily as a means to an end. We're encouraged to build as a part of something greater: business, financial systems, social movements, and political statements. It's important to ground these aims in craftsmanship and the simple joy of having built something not just functional, but imbued with care and elegance. The effort to construct each piece of a system to be in alignment with the others is a source of pride, and is worthwhile even at the cost of other material rewards.
We've been building the protocols described here (Polkadot) for over 5 years, and I chose to end this post this way to answer the question many readers will have: "Why would anyone spend 5 years doing this?". This is a message to all new joiners in the crypto space. This is for everyone who's been riding the waves since the surges of 2020. If you find yourself seeking a sanctuary from the greed and the fray, it exists, and it's been here the whole time.
Full Disclosure / Important Disclaimer: Signum Growth Capital and its Founder/CEO are biased, having voted with our feet in working for the Web3 Foundation as Advisor since November of 2019.